Latex Workshop for Research Paper Writing
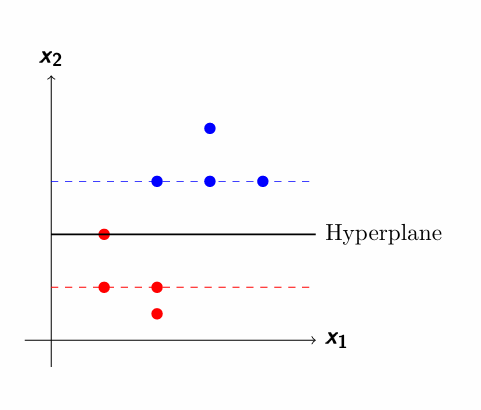
Workshop Detail Presentation Resources Latex Tutorials 1-https://www.bu.edu/math/files/2013/08/ShortTeX3.pdf 2-https://cdn.overleaf.com/static/latex/learn/free-online-introduction-to-latex-part-1.pdf 3-https://tobi.oetiker.ch/lshort/lshort.pdf Latex Diagrams Tikz Package 4-https://tug.ctan.org/info/visualtikz/VisualTikZ.pdf 5-https://www.bu.edu/math/files/2013/08/tikzpgfmanual.pdf See Also: Beamer Latex Code to Explain Variance What is Research? How to Write a Research Paper
Latex Workshop for Research Paper Writing Read More »